How to Perform Compliance Gap Analysis
Rudramuni Swamy H M | 12 Dec 2025 | Not Modified
Compliance Gap Analysis has become a mission-critical process for organizations navigating increasingly complex regulatory, security, and industry-specific standards. Whether you operate in fintech, SaaS, healthcare, BFSI, manufacturing, or cybersecurity services—the ability to identify compliance gaps early can protect your business from penalties, breaches, and operational disruptions.
In this blog post, we will break down what compliance gap analysis is, why it matters, step-by-step instructions to perform it effectively, plus templates, examples, and best practices.
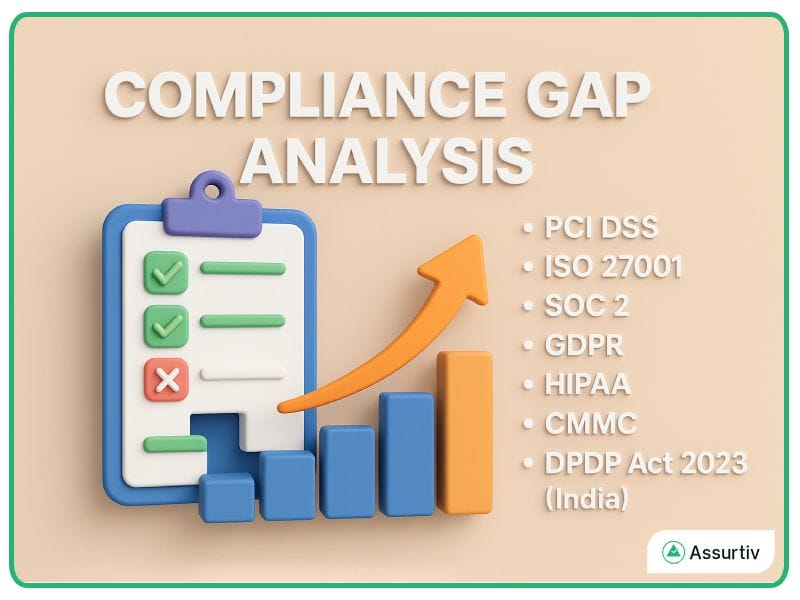
What Is Compliance Gap Analysis?
A Compliance Gap Analysis is a structured assessment that compares your current security, operational, or regulatory posture against a required standard or framework.
It highlights what you have, what you lack, and what must be improved to achieve full compliance.
This assessment is widely used across frameworks such as:
- PCI DSS
- SOC 2
- GDPR
- CMMC
- DPDP Act 2023 (India)
It acts as the roadmap to get compliance by identifying controls, processes, documentation, or technical requirements that need enhancement.
Why Is Compliance Gap Analysis Important?
A robust compliance gap assessment helps organizations:
- Prevent costly violations and fines
- Strengthen security posture
- Build trust with customers, partners, and regulators
- Streamline certification or audit readiness
- Prioritize high-risk compliance areas
- Reduce compliance workload through better planning
In short—it gives clarity, direction, and measurable insights into your compliance journey.
What Does “Gap” Mean in Compliance?
A gap in compliance refers to any control, policy, process, or technical requirement your organization does not meet when compared to a regulatory, industry, or internal standard.
Examples of compliance gaps include:
- Missing policies (e.g., no Access Control Policy for ISO 27001)
- Lack of evidence logs (e.g., SOC 2 audit trails)
- Incomplete vendor risk assessments
- Missing encryption or MFA
- No dedicated incident response plan
- Roles and responsibilities not defined
- Lack of training and awareness documentation
These gaps form the foundation of improvement planning.
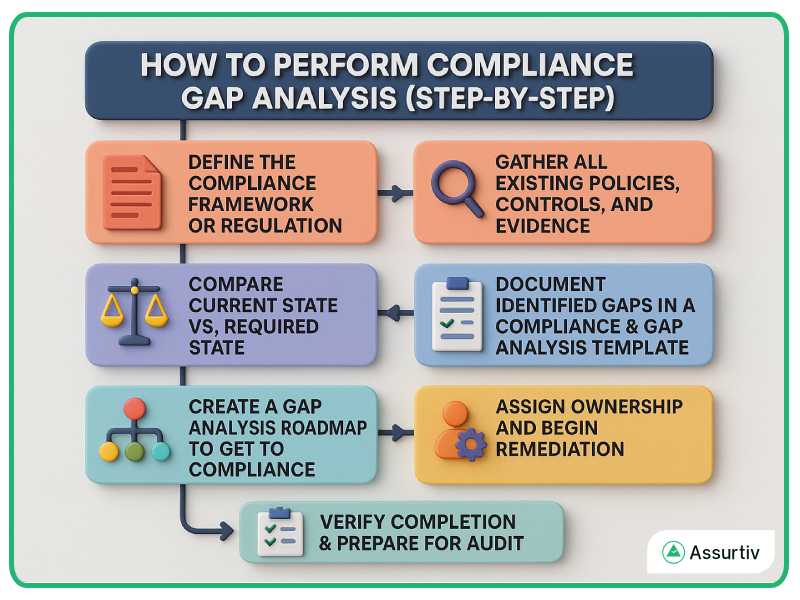
How to Perform Compliance Gap Analysis (Step-by-Step)
 Step 1 — Define the Compliance Framework or Regulation
Step 1 — Define the Compliance Framework or Regulation
Begin by clearly identifying the requirements you are measuring against. This may include:
- PCI compliance gap analysis (payment security)
- ISO 27001 readiness assessment
- CMMC compliance gap analysis service (for defense sector vendors)
- GDPR or DPDP data privacy compliance
- Industry-specific regulatory compliance gap analysis
Document scope, applicability, and audit boundaries.
Step 2 — Gather All Existing Policies, Controls, and Evidence
Collect internal documentation such as:
- Security policies
- SOPs and procedures
- Logs and monitoring reports
- Access controls
- Risk assessments
- Vendor assessments
- Asset inventory
- Incident response reports
This becomes your baseline for the assessment.
Step 3 — Compare Current State vs. Required State
This is the core of regulatory compliance and gap analysis.
Match every requirement of the selected framework with your existing controls.
For each item, mark it as:
- Compliant
- Partially compliant
- Non-compliant
- Not applicable
This step identifies high-risk and high-priority areas.
Step 4 — Document Identified Gaps in a Compliance & Gap Analysis Template
Create a structured matrix that includes:
What to Include in Your Gap Analysis Template
- Requirement ID
- Requirement description
- Current status
- Evidence available
- Gap identified
- Gap severity (High, Medium, Low)
- Owner
- Remediation Timelines
- Required actions
- Dependencies
Many organizations still today, maintain this in a spreadsheet but to stay ahead in the industry few of them implement this with GRC tool. So what about your organisation?
Step 5 — Create a Gap Analysis Roadmap to Get to Compliance
Once you have the list of gaps, you must build a prioritized roadmap that includes:
- Policy creation
- Technical configurations
- Risk mitigation
- Process improvements
- Employee training
- Documentation updates
- Vendor or third-party compliance measures
The roadmap should specify:
- Deadlines
- Resource allocation
- Dependencies
- Ownership
- Expected outcomes
This roadmap makes the path to compliance trackable and auditable.
Step 6 — Assign Ownership and Begin Remediation
Every gap needs an accountable owner.
Typical owners include:
- CISO
- Compliance Manager
- IT Manager
- Risk Owner
- Process Owner
A clear RACI model helps avoid gaps falling through the cracks.
Step 7 — Verify Completion & Prepare for Audit
Once remediation is completed:
- Validate evidence
- Perform internal audits
- Re-run the gap assessment
- Ensure documentation and logs are in place
- Align with auditor expectations
This step confirms readiness for certification or regulatory evaluation.
Examples of Gap Analysis in Compliance
Here are common real-world illustrations:
PCI DSS
Gap: No quarterly external vulnerability scans
Fix: Implement ASV scans + track results in a GRC tool
SOC 2 Type II
Gap: Missing access reviews
Fix: Implement monthly or quarterly access review workflow
ISO 27001
Gap: No formalized risk assessment process
Fix: Adopt a consistent methodology + maintain evidence
CMMC Level 2
Gap: No multi-factor authentication
Fix: Enforce MFA across all endpoints + cloud systems
Best Practices for an Effective Compliance Gap Analysis
- Use evidence-driven assessment, not assumptions
- Keep documentation centralized
- Align gap severity with business risk
- Use automation tools or GRC platforms
- Update your gap analysis template yearly
- Map controls across frameworks to reduce workload
Conclusion
Performing an effective Compliance Gap Analysis is one of the fastest ways to strengthen your governance, risk, and compliance strategy. By understanding where your organization stands today and what gaps exist, you can build a clear, actionable roadmap to achieve full compliance—whether for PCI, ISO, SOC 2, CMMC, GDPR, or industry regulators.
Implement the steps outlined above to reduce audit fatigue, save costs, and shorten your compliance timeline with confidence.

 Step 1 — Define the Compliance Framework or Regulation
Step 1 — Define the Compliance Framework or Regulation