How to Build an Effective Cyber Incident Response Plan in 2026
Chakrapani KVC | 9 Dec 2025 | Not Modified
Cyberattacks in 2026 are not just more frequent — they are more sophisticated, automated, and faster than ever before. Ransomware-as-a-service, AI-enabled phishing, deepfake scams, supply-chain breaches, and data exfiltration attacks have reshaped global security priorities.
To survive this evolving threat landscape, every organization — whether a startup, enterprise, or government agency — must have a robust cyber incident response plan that prepares teams to identify, contain, and recover from cyberattacks with precision and speed.
Here, we have explained how to build a future-ready, effective, and compliant cyber security incident response plan designed specifically for 2026.
Why a Cyber Incident Response Plan Is Crucial in 2026
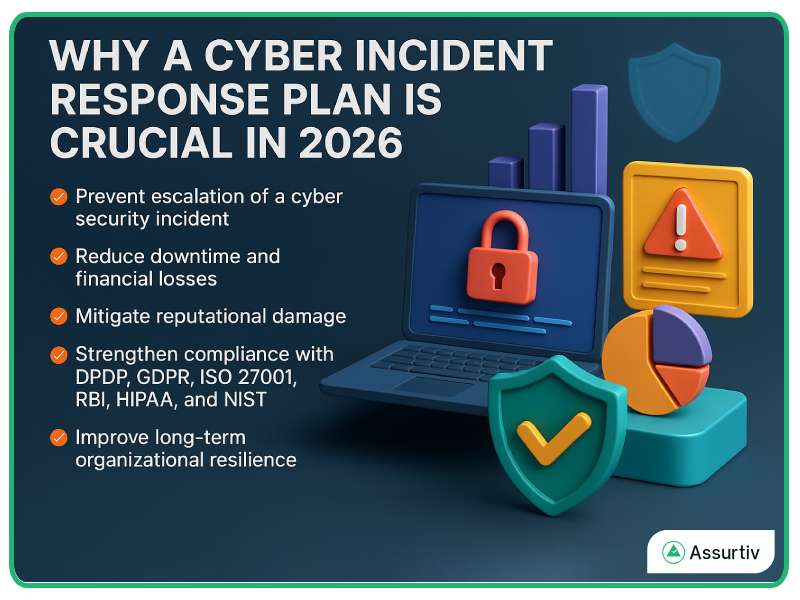 A well-designed incident response in cyber security framework helps organizations reduce damage, avoid regulatory penalties, and maintain business continuity. With rising attack velocity and increasingly complex digital ecosystems, businesses must move from reactive defence to proactive, structured response.
A well-designed incident response in cyber security framework helps organizations reduce damage, avoid regulatory penalties, and maintain business continuity. With rising attack velocity and increasingly complex digital ecosystems, businesses must move from reactive defence to proactive, structured response.
A strong cyber incident response strategy helps you:
- Prevent escalation of a cyber security incident
- Reduce downtime and financial losses
- Mitigate reputational damage
- Improve long-term organizational resilience
For all industries — especially BFSI, SaaS, healthcare, retail, and critical infrastructure — a mature incident response cyber security approach is non-negotiable.
Key Components of an Effective Cyber Incident Response Plan
 A successful plan is built on people, processes, and technology working in sync.
A successful plan is built on people, processes, and technology working in sync.
Below is the modern 2026-ready framework.
Preparation – Establishing Readiness Before Attacks Occur
Preparation forms the backbone of your entire cyber security incident response plan. It includes:
- Defining roles and responsibilities for your incident response team
- Creating standard operating procedures for detection and escalation
- Ensuring regularly tested backups
- Deploying monitoring tools such as Semgrep, Trivy, Microsoft Cloud, Grafana
- Conducting periodic training and simulations
- Establishing a 24/7 communication protocol
The better your preparation, the faster your organization can contain a cyber incident.
Detection – Identifying a Cyber Incident Early
In 2026, early detection is essential because attacks spread rapidly. Organizations must use advanced tools that identify:
- Unusual network traffic
- Credential misuse
- Malware signatures
- Suspicious API activity
- Data exfiltration behaviour
AI-augmented alerts and behavioural analytics help teams recognize threats quickly and accurately — the cornerstone of modern cyber incident response.
Analysis – Understanding the Scope and Impact
Once an incident is detected, your team must determine:
- How the attack is originated
- Which systems are affected / System Impact Analysis
- The attacker’s intent
- Whether data has been compromised
- Potential business impact
Comprehensive analysis ensures targeted containment instead of blind disruption.
Containment – Preventing Further Spread
Containment stops cyber incidents from escalating. This includes:
- Isolating compromised endpoints
- Blocking malicious traffic
- Suspending affected user accounts
- Disconnecting critical systems from the network
Short-term containment stabilizes your environment, while long-term containment ensures attackers cannot regain access.
Eradication – Removing the Threat Completely
This stage focuses on eliminating the root cause:
- Removing malware or infected components
- Patching vulnerabilities
- Resetting credentials
- Hardening configurations
- Applying additional monitoring
Eradication ensures your organization is not vulnerable to repeated attacks.
Recovery – Restoring Business Operations
Recovery includes:
- Restoring systems and data from clean backups
- Rebuilding affected machines
- Validating system integrity
- Monitoring for additional threat activity
A recovery plan must balance speed with security to avoid reintroducing vulnerabilities.
Lessons Learned – Strengthening the Response Maturity
Post-incident review helps teams understand:
- What went wrong
- What worked well
- What must improve
- How to update the cyber incident response plan
- What new controls are required
This step converts incidents into organizational intelligence.
Communication During Cyber Incidents (A Critical Component)
Clear communication reduces panic, misinformation, and operational confusion. Your plan must include communication guidelines for:
- Internal teams
- Executives and board members
- Regulators and authorities
- Customers and stakeholders
- Media and external partners
A structured communication chain ensures timely, accurate, and strategic messaging, especially during high-impact cyber security incidents.
Tools & Services That Strengthen Cyber Incident Response in 2026

Modern response plans rely heavily on automated and AI-driven tools. Essential technologies include:
- SIEM for threat monitoring
- SOAR for automated playbooks
- XDR for endpoint and network visibility
- Threat intelligence feeds
- Cloud-native detection systems
- Incident response retainer services
Many organizations also choose external cyber incident response services for rapid remediation and 24/7 support.
Best Practices for a Future-Ready Cyber Incident Response Plan
To ensure your plan can handle 2026-level cyber threats:
- Keep your documentation updated
- Test the plan quarterly
- Maintain an always-ready IR team
- Integrate automation wherever possible
- Strengthen third-party incident response roles
- Align your plan with frameworks like NIST CSF, ISO 27035, and SOC2
A future-ready plan is dynamic, scalable, and always evolving.
Your Cyber Resilience Starts with an Effective Response Plan
A well-defined cyber incident response strategy determines how successfully your organization can withstand and recover from modern cyberattacks. In 2026, with threats growing rapidly and compliance pressures rising, your response plan must be proactive, automated, and continuously improved.
By strengthening your preparation, detection, communication, and recovery capabilities, you not only reduce damage but also build long-term trust with customers, regulators, and stakeholders.
Cybersecurity resilience in 2026 begins with one thing: a powerful, effective, and future-ready cyber incident response plan.